Cyber Threat Intelligence (CTI) is the process of collecting, analyzing, and applying data on cyber threats, adversaries, and attack methodologies to transform raw data into actionable insights that enable organizations to anticipate, detect, and respond to risks proactively.
Digital transformation globally is not a thing of the distant future, it’s happening right now as we speak. With constant evolution in technology, an unlimited amount of data is processed every day in businesses and corporations. Now, this data is a gold mine for cyber attackers. Cyber threats are evolving at such a fast rate that if organizations don’t modernize their cyber defences, they will keep facing financial and reputational losses with thousands of attacks daily. This is where cyber threat intelligence (CTI) comes into the picture.
If you are wondering what cyber threat intelligence is, it is a strategic set of processes where cyber professionals collect and analyze data about potential cyber threats so they can make faster decisions in case of any cyber attacks in the future. In simple terms, we can say that CTI is all about converting insights gathered from past cyber attacks to create actionable steps to prevent attacks.
What is Cyber Threat Intelligence?
Cyber Threat Intelligence (CTI) refers to the overall process of collecting valuable information on how a potential cyber threat works, how they breach the system to steal data, and analyzing the data to prevent future potential attacks.
The CTI’s meaning goes beyond just raw data usage. Using valuable insights gathered from past attacks’ data, organizations use threat intelligence in cyber security to predict and prevent future threats before they happen.
Cybercrime incurs huge financial losses, with an estimated amount exceeding $10.5 trillion annually. CTI acts as a barrier between threats and sensitive data and acts as a critical component of modern cybersecurity strategies.
Why Is Cyber Threat Intelligence Important in Cybersecurity?
Unlike cyber threats in the past, modern attacks are specifically targeted and are constantly evolving. With different attack variations being performed for different types of vulnerabilities, threat intelligence in cybersecurity plays a crucial role in controlling these attacks.
CTI helps organizations to increase their cyber defenses and be proactive when facing any cyber threats. Instead of waiting for an attack to happen, CTI teams can anticipate risks based on attacker behavior and threat trends globally.
Decision-making is also improved through the context provided, that is, who is attacking, why they are attacking, and how they operate. This important information helps security teams to prioritize threats effectively. In today’s world, where thousands of new threats are emerging every single day, understanding what is cyber threat intelligence is essential to stay ahead of the attackers.
Also read: Cyber Hygiene Best Practices
Types of Cyber Threat Intelligence
There are different types of cyber threat intelligence, each serving a specific purpose in cybersecurity.
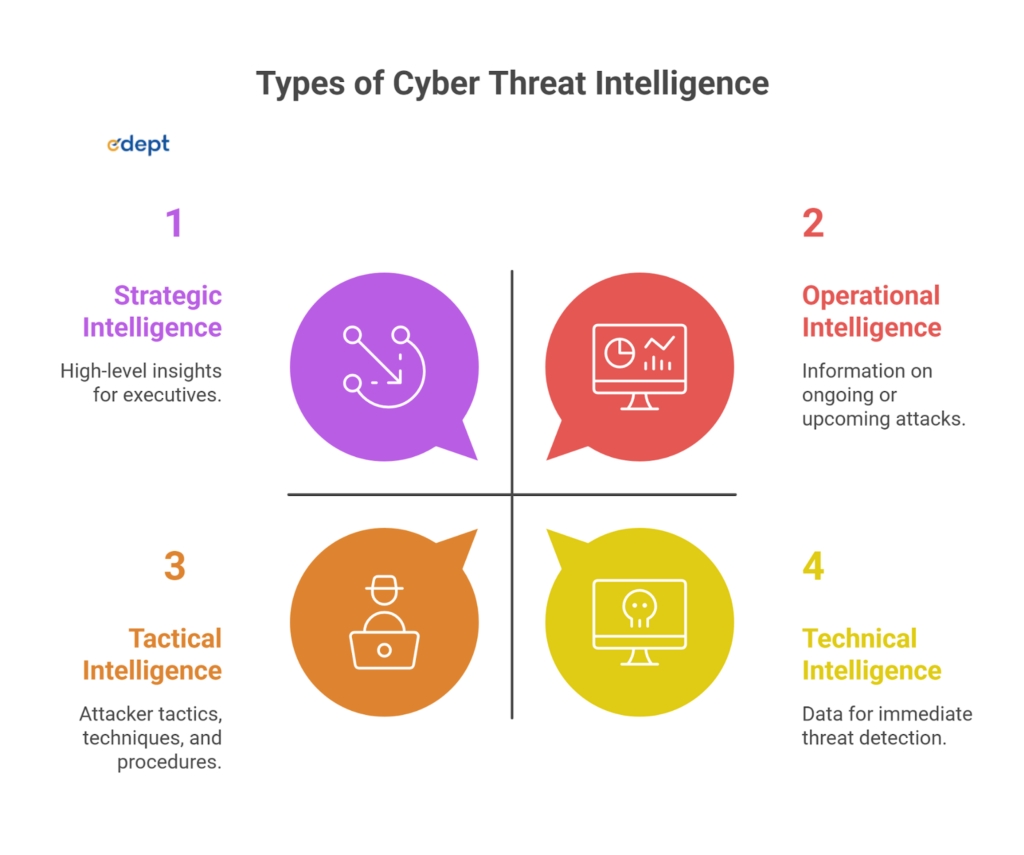
Strategic Threat Intelligence
This focuses on high-level insights for executives. It includes trends, risks, and long-term threat landscapes to support business decisions.
Operational Threat Intelligence
This type of CTI team provides information about any ongoing or upcoming attacks. Using info in real-time, they help teams understand attacker intent, targets, and timings.
Tactical Threat Intelligence
Their main working pillars are TTPs, which are attacker tactics, techniques, and procedures. It helps security teams strengthen defenses against specific attack methods.
Technical Cyber Threat Intelligence
Technical intelligence includes data like IP addresses and malware signatures, which is used for immediate detection and blocking of threats.
Benefits of Cyber Threat Intelligence
Cyber threat intelligence goes beyond just identifying threats, but also helps organizations build a structured and resilient security strategy. By using threat intelligence in cybersecurity, smarter decisions are made by businesses in fighting against cyber threats, which ultimately safeguard their data and prevent financial losses. Let’s look at some benefits of CTI one by one.
Increased Visibility
CTI provides a clear view of how threats can attack the vulnerabilities. It includes attacker behavior, targets, and all the upcoming risks. This clear vision helps organizations understand where they are unsafe and vulnerable.
Enhanced Threat Detection
Security teams can identify any suspicious activity with real-time insights, even before they spread and infects the systems. This significantly reduces the chances of successful attacks and losses.
Stronger Security Posture
With the insights gained on malware practices through CTI teams, organizations can create their own security measures with actual threat patterns instead of relying on generic protections.
Reduced Risk
By having a scripted pattern of all the vulnerabilities and attack methods noted in advance, CTI helps minimize the damage caused by cyber attackers.
Informed Decision-Making
With a clear plan in sight, leaders can make data-driven decisions on all the security aspects of the organization, like investments, policies, and priorities, using actionable intelligence. This free space to think is crucial for the growth of businesses without thinking twice about their data safety.
Accelerated Incident Response
CTI enables fast detection and response to enable damage control. This helps teams to contain threats before they escalate into something major. This is crucial as faster detection enables the malware from spreading into the system through the breach, thus saving the business in safeguarding their data while keeping their daily workflow going.
Cost Efficiency
If an attack has already happened with significant losses both financially and data-wise, containing the threat and recovering from it is quite expensive. This is the reason CTI prevents these breaches even before they cause any havoc, which is cheaper, saving the company from losses. This makes CTI a cost-effective cybersecurity investment.
Key Sources of Threat Intelligence
Effective threat intelligence in cybersecurity depends entirely on collecting data from multiple reliable sources. The more reputation the source has, the better the insights. Having a good understanding of these sources is very important to fully grasp what cyber threat intelligence is in practice.
Let’s see some key sources important for Cyber Threat Intelligence:
- Dark Web Monitoring: It tracks hacker activities, any leaked data, and all the discussions in underground marketplaces.
- Open-Source Intelligence (OSINT): These are open-sourced and publicly available data, such as blogs, forums, research papers, and security reports.
- Internal Security Data: Logs, alerts, and past incidents within an organization provide valuable context for detecting threats.
By combining these reliable sources, organizations, with the help of CTI teams, can develop a structured threat intelligence framework that strengthens the overall security of their businesses.
Also Read: Mastering Hacking Tools
Challenges in Cyber Threat Intelligence
Cybersecurity threat intelligence has large benefits, but it also has its own drawbacks. For example, one of the biggest problems is that there are so many sources of data that you quickly become overwhelmed by too much information, and turning that large source of information into usable pieces is hard to process.
Another challenge is data reliability. Not all sources are accurate, and sometimes false positives lead to the wastage of time and resources. Working to neutralize a threat that was not there in the first place is a loss for everyone. Additionally, integrating CTI into existing security systems requires skilled professionals and proper tools.
As cyber threats continue to change and develop, the need to keep intelligence updated gets harder. If there is no continuous monitoring of threats and suspicious analytical activity, even the best sources of intelligence will soon become outdated and ineffective.
Conclusion
Cyber threats are advancing as we talk with each passing day, and are becoming more sophisticated. This makes traditional security approaches less effective. Understanding what is cyber threat intelligence helps organizations to shift from generic security thinking to proactive protection. With the help of the right intelligence from reliable sources, businesses can identify risks early and respond faster, which decreases the damage.
The real value of CTI lies in how it is applied. From improving detection to reducing risks, the benefits of cyber threat intelligence make it an integral part of modern cybersecurity.
The success entirely depends on using accurate data, using the right tools, and having skilled professionals. In today’s evolving threat landscape, cyber threat intelligence is becoming a necessity for businesses.
Related Links:
| Real Life Cyber Attack Case Studies | Application Security Complete Guide |
| Data-driven Business Management | Role of AI in Cybersecurity |
FAQs of Cyber Threat Intelligence
What are the 3 main types of threat intelligence?
The 3 main types of threat intelligence include strategic, operational, and tactical threat detection. Each of these types serves its own purpose of decision-making and security operations.
Is cyber threat intelligence a good career?
If you love solving problems and working with data, cyber threat intelligence is a great career with high demand globally. Organizations need skilled professionals to analyze and respond to evolving attacks.
What is cyber threat analysis?
Cyber threat analysis is a process of examining data and insights gained from threats to understand how attacks actually happen in real time, and to have a future-proof plan to stop these attacks.
How do you select a Threat Intelligence Platform?
Choice is entirely based on data accuracy, integration capabilities, automation features, and ease of use.
How to use Cyber Threat Intelligence?
Cyber threat intelligence is mainly used to stop any type of malware attacks and prevent any losses for the organizations.
What does a Cyber Threat Intelligence analyst do?
The main work of a cyber threat intelligence analyst involves collecting data and insights from real threats, detecting real-time threats even before they breach and spread in the systems, and responding bravely against cyber threats with effectiveness.