With the rapid rise of digital transformation, cloud security is becoming a critical pillar for organizations as they move their operations to cloud platforms. Understanding how cloud security works helps organizations and professionals protect sensitive data and ensure infrastructure security against evolving cyberattack threats.
Modernization of cloud security architecture involves operations such as identity management, encryption, data monitoring, and layered protection strategies to secure cloud environments effectively. Organizations are implementing strong cloud security best practices to ensure safe data transactions and maintain business continuity.
In this guide, we will examine the operation, layers, risks, and future of cloud security in a structured, practical manner.
Introduction to Cloud Security
Cloud security refers to the technologies used to protect sensitive data by using policies and cloud-based systems and applications. Cloud security systems, if implemented well, will ensure secure access, data protection, and threat prevention across cloud environments.
With rapid advances in cyber threats, implementing robust cloud security strategies is increasingly crucial for organizations to protect their assets and safeguard their digital data against cyberattacks. Multiple cloud vendors promote their security systems with either one-time payments or subscription models based on the number of security layers and available benefits.
In 2026, if you are not using cloud security to protect your assets, you are more vulnerable to cyber incidents compared to those who implement it in their daily operations.
How Cloud Security Works
Cloud security is a vast field, and its working involves multiple coordinated processes that protect users, their data, and systems at every level.
Step-by-Step Process of Cloud Security
We got to know what cloud security is, an interconnected model of devices and cloud servers protecting your sensitive data and devices from cyber threats. Now let’s see the exact step-by-step process of how cloud security works to safeguard your assets.
Identity Verification
The first step in implementing cloud security to protect a system or data starts with verifying the user’s identity using their credentials, biometrics, or authentication factors. Using these verification methods ensures that only the registered user can access their data, reducing the risk of identity theft and data loss from unauthorized access.
Access Control
Access Control checks what a user can do within the cloud environment. Role-based access to cloud resources reduces the risk of unauthorized access and account compromise.
Data Encryption
Encrypting your sensitive data protects it at rest and in transit. Even if attackers intercept the data, encryption ensures it remains unreadable without the decryption keys, thereby enhancing overall data security.
Continuous Monitoring
Cloud environments are continuously monitored to detect anomalous activity. Various security tools detect threats in real time, enabling rapid data breach quarantining and preventing data loss.
Core Components of Cloud Security
Identity and Access Management (IAM)
IAM controls user identities and permissions. It also ensures that only authorized users can access resources, thereby enabling strong authentication and reducing both internal and external threats.
Encryption
Encryption involves converting data into unreadable formats so even if attackers get access to your data, they won’t be able to read through it. It protects sensitive data from unauthorized access during storage and transmission across cloud systems.
Network Security
Important network security assets include firewalls, virtual networks, and segmentations. These tools protect cloud infrastructure from external attacks and unauthorized access attempts.
Security Monitoring Tools
Keeping the system monitored by using tools to track unusual activities and detect anomalies before any cyber incident happens. This way, you can save your sensitive data and prevent identity theft.
Cloud Security Architecture and Layers
Cloud security systems use layered controls that work together to protect data and systems across cloud environments. Let’s go through those security layers in cloud architecture.
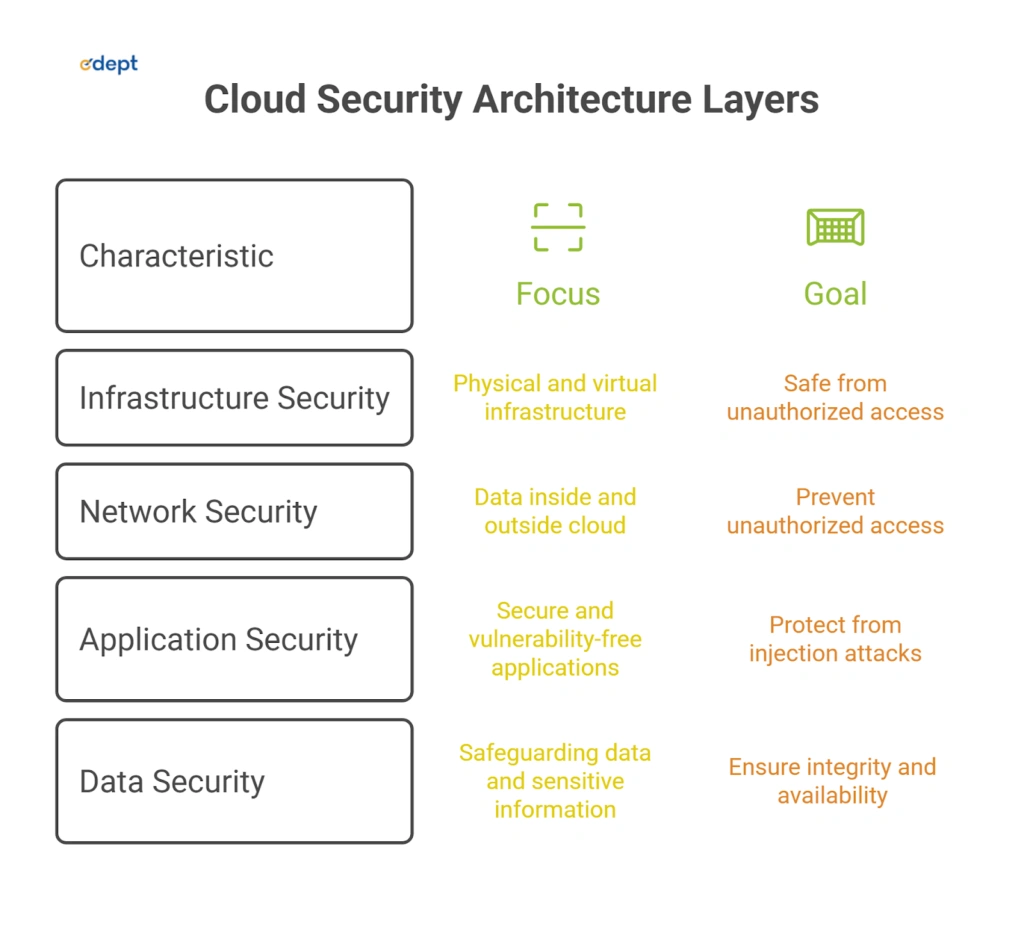
Infrastructure Security
This layer primarily focuses on securing physical and virtual infrastructure, including servers and storage systems. It also ensures that cloud environments remain secure against unauthorized access and hardware-level vulnerabilities.
Network Security
Network security protects data inside and outside the cloud using firewalls, VPNs, and traffic filtering. It prevents unauthorized access and ensures secure communication between cloud services.
Application Security
Application security ensures applications are secure and free of vulnerabilities. Using regular testing, patching, and secure coding practices helps protect applications against threats such as injection attacks and unauthorized access.
Data Security
Data security focuses on safeguarding data and sensitive information through encryption, backups, and access controls. It also ensures integrity and availability across cloud environments.
The Shared Responsibility Model in Cloud Security
The shared responsibility model in cloud security defines the division of security responsibilities between cloud providers and customers. Cloud providers manage infrastructure security, hardware security, and core services, while customers are responsible for securing data, applications, and user access. Getting to know this model is essential to prevent security lapses and ensure complete protection in cloud environments.
Common Cloud Security Risks
Cloud environments face multiple threats and risks that can compromise data, systems, and applications if not managed properly. Let’s see some common ones that cloud security experts work hard to control.
Data Breaches
Data breaches are common when unauthorized users gain access to sensitive information. Weak access controls, inadequate encryption, and credential mismanagement increase the risk of data exposure.
Misconfigured Cloud Settings
Bad configurations like open storage buckets or weak permissions are one of the most common cloud security risks. These mistakes can lead to data leaks on the public internet.
Insider Threats
Sometimes, within an organization, employees or authorized users may misuse access privileges, either intentionally or accidentally. Insider threats can lead to data leaks, identity theft, and system damage, and should be addressed by cloud security experts.
Malware and Ransomware
Malware attacks and Ransomware attacks are very common ways used by cyber attackers to infect cloud systems. These attacks can encrypt data, disrupt services, and cause financial and operational damage.
Best Practices for Cloud Security Implementation
Implementing robust cloud security practices helps organizations reduce risk and strengthen their defenses against cyber threats. Let’s review key practices to keep your cloud environment secure from cyberattacks.
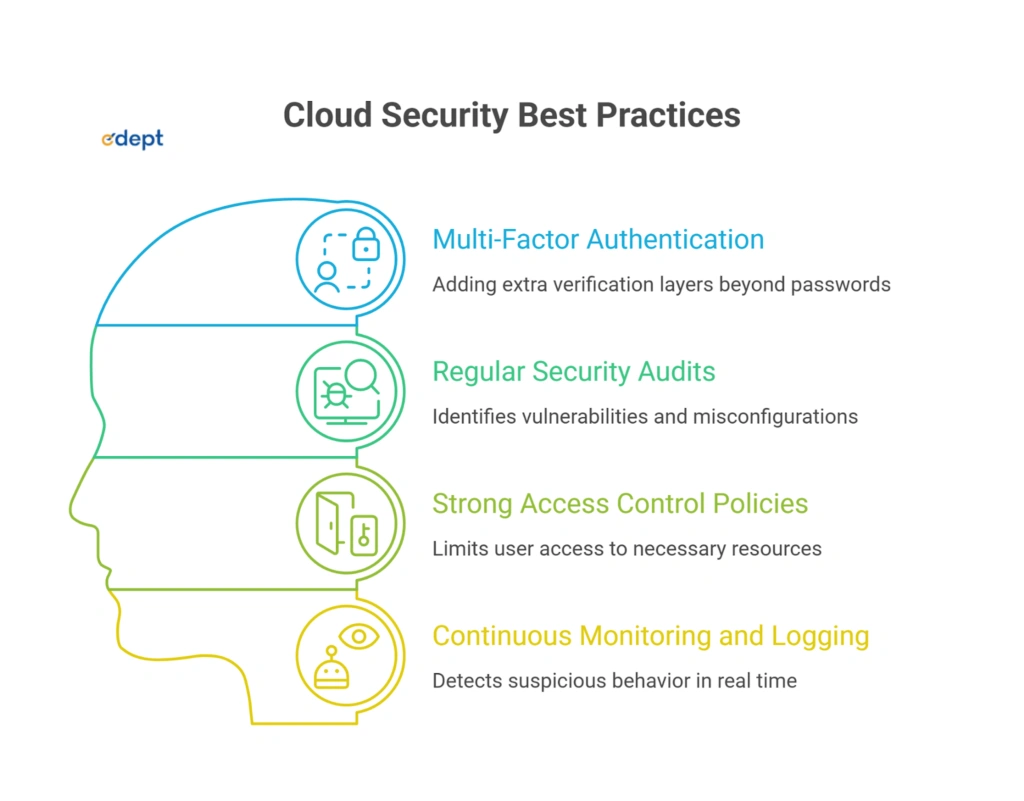
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by adding extra verification layers beyond passwords. This significantly reduces the chances of unauthorized access.
Regular Security Audits
Regular audits keep track of any suspicious attacks, identify vulnerabilities, misconfigurations, and security gaps. Organizations can fast-track and fix issues before they escalate further and damage overall cloud security posture.
Strong Access Control Policies
Applying strict access control allows users to access only what they need. This reduces insider risk and limits damage in the event of compromised accounts.
Continuous Monitoring and Logging
Monitoring and logging activities help detect suspicious behaviour in real time. This ensures faster response to threats and improves incident management.
Cloud Security Tools and Technologies
Modern cloud environments rely on advanced tools to monitor, manage, and secure systems effectively.
Cloud Access Security Brokers (CASB)
CASB is a security layer between users and cloud services. They implement all the security policies, monitor activities, and protect sensitive data across multiple cloud platforms.
Cloud Security Posture Management (CSPM)
CSPM tools track any misconfiguration and compliance risks. They continuously assess cloud environments and also provide recommendations to improve security posture.
Cloud Workload Protection Platforms (CWPP)
CWPP is a set of tools that manages workloads such as virtual machines and containers. They monitor unusual behaviors, detect threats, and quarantine them to ensure runtime security across cloud environments.
Secure Access Service Edge (SASE)
SASE is a unified model that combines networking and security. It provides secure access to cloud applications while complying with security policies across cloud environments.
Challenges in Cloud Security and Their Solutions
Cloud security presents its own challenges that can disrupt systems and servers, but reliable cloud experts can easily address them. Common challenges include misconfigurations, limited visibility, and evolving cyber threats. Organizations often struggle to manage large-scale environments while ensuring compliance. To address these challenges, organizations implement measures such as automated monitoring, zero-trust architectures, investments in skilled professionals, and adherence to structured cloud security frameworks to strengthen protection and reduce risk.
Future Trends in Cloud Security
Advances in cloud security and digital transformation are enhancing protection mechanisms and threat detection capabilities. The global cloud computing market was valued at $912.77 billion in 2025 and is projected to reach $1.614 trillion by 2030, growing at a compound annual growth rate (CAGR) of 17.43% through 2032, according to Precedence Research and Statista. This shows the trends in cloud security that are evident in the current market.
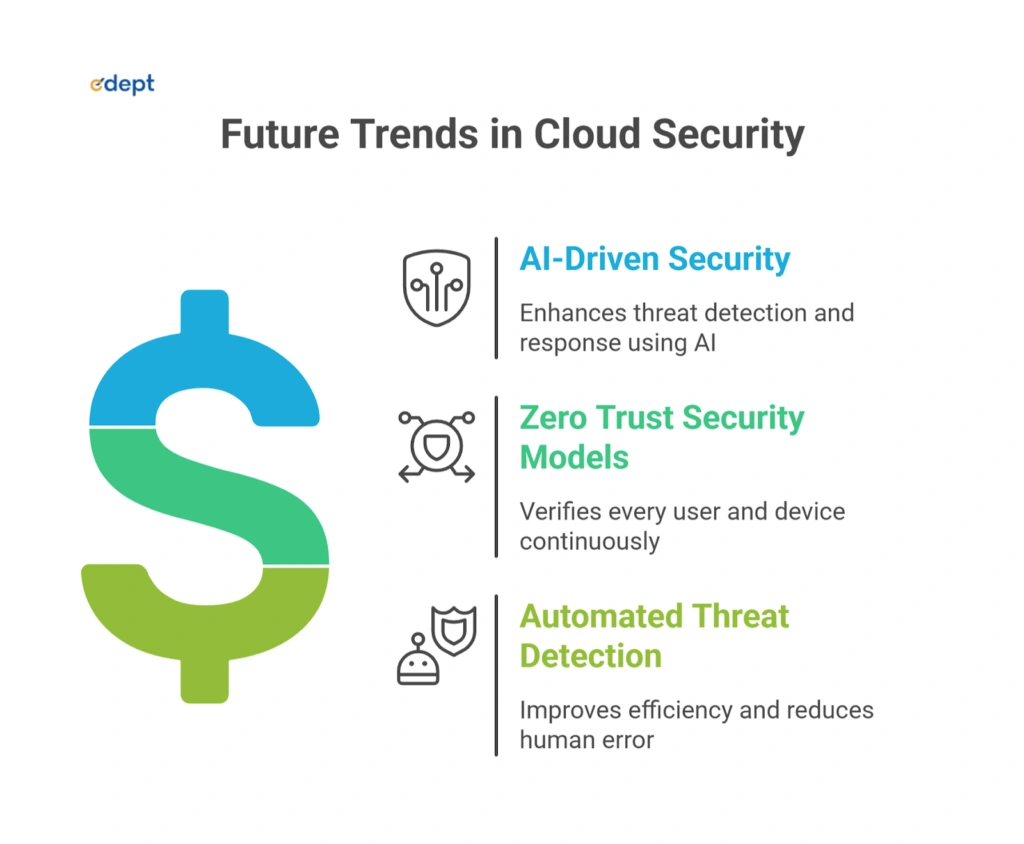
AI-Driven Security
In the current cloud security landscape, AI is transforming the industry at a rapid pace. AI enhances cloud security by analyzing large datasets to detect anomalies and predict threats. It also ensures faster response and proactive defense against advanced cyber threats.
Zero Trust Security Models
Zero-trust security models ensure trust by verifying every user and device continuously. It also strengthens access control and significantly reduces the risk of unauthorized access in cloud environments.
Automated Threat Detection
Automation improves threat detection by continuously monitoring systems and responding to unwanted or suspicious activity instantly. Automation significantly reduces human error and enhances overall security efficiency.
Final Verdict: Importance of Cloud Security in Data Safety
In this guide, we learned what cloud security is and how it protects users and organizations from cyber threats. As a multi-layered model, cloud security combines identity management, encryption, monitoring, and strong policies to protect digital assets. Having a good understanding of how cloud security works helps organizations take necessary steps to protect their assets and build resilient systems. By following best practices and adopting modern tools, businesses can ensure secure and efficient cloud operations.
| Mastering Hacking Tools: A Complete Guide for Everyone | Role of Cybersecurity in the Metaverse & Web 3.0 |
| Role of AI in Cybersecurity | The Impact of 5G on Cybersecurity Threats and Solutions |
FAQ’s of Cloud Computing Security
What is the shared responsibility model in cloud security?
The shared responsibility model in cloud security distributes security responsibilities between the provider and the customer (data, access, applications) to ensure clear accountability in cloud environments.
How does zero-trust differ from traditional perimeter security?
Zero-trust continuously validates every request, unlike traditional models that trust users within the network boundary.
What are free tools for basic cloud security audits?
Some free cloud security tools include AWS Trusted Auditor, Azure Security Center (basic), and open-source scanners that help identify misconfigurations and vulnerabilities.
Why encrypt data both at rest and in transit?
Encryption protects data by rendering it unreadable to unauthorized parties, preventing access during storage and transmission, and ensuring confidentiality and compliance.
How can businesses improve cloud security?
By implementing MFA, monitoring systems, regular audits, strong access controls, and zero-trust security models, organizations can enhance cloud security and safeguard their data.