It is hard to imagine modern business running without the cloud at this point. Organizations today rely on it for everything from storing sensitive data to managing entire operations. But that growth comes with a serious concern. Gartner projects global cloud spending to exceed $675 billion in 2024, and IBM reports that the average cost of a cloud-related data breach hit $4.45 million in 2023. The stakes have never been higher.
So, what is cloud security? It is the combination of technologies, policies, and practices that protects cloud-based systems, data, and infrastructure from cyber threats.
In this blog, we will cover the types, key benefits, and career opportunities in this rapidly growing field.
What Is Cloud Security?
At its most basic level, cloud security involves the technologies, policies, and controls that organizations use to protect their cloud environments from threats, unauthorized access, and data loss. The cloud security definition goes beyond just installing a firewall or setting a password. It includes cloud security technologies such as encryption, identity management systems, real-time monitoring platforms, and network firewalls, all working together to provide a secure foundation for cloud operations. Every layer plays a role, and when they work together, they provide organizations with a much stronger defence against the attacks that are becoming more common every year.
Types Of Cloud Security
Cloud security is not a single tool or a single policy. It is built in layers, each one designed to protect a different part of the cloud environment.
Network Security
Network security focuses on protecting how information flows within cloud environments. Firewalls, intrusion detection systems, and secure gateways work together to monitor traffic, flag suspicious activity, and prevent unauthorized users from accessing the network.
Application Security
Applications running in the cloud face their own set of risks. Application security is about finding and fixing vulnerabilities before attackers can exploit them. Secure coding practices, vulnerability testing, and runtime protection are essential to keeping cloud applications safe.
Data Security
Data is often the primary target of cyberattacks, making data security one of the most critical layers of cloud protection. Encryption, tokenization, and backup systems protect sensitive information, whether it is at rest or in transit between systems.
Identity And Access Security
Not everyone who accesses a cloud system should have the same level of access. Identity and access security ensure that only the right people can access the right resources. Authentication protocols, role-based access controls, and identity verification all help prevent unauthorized access.
Benefits Of Cloud Security
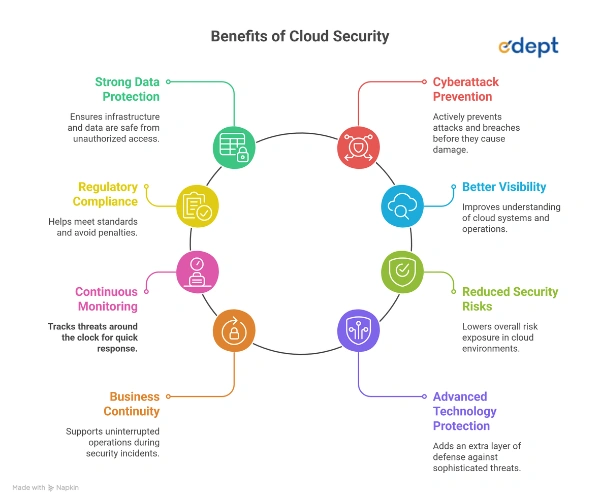
Investing in cloud security delivers real, measurable benefits for organizations of all sizes. Here are some of the most important benefits:
- Strong Data Protection: Cloud security safeguards your infrastructure and stored data against unauthorized access and other threats.
- Cyberattack Prevention: It proactively prevents cyberattacks, data breaches, and unauthorized access before they cause damage.
- Regulatory Compliance: Cloud security helps organizations meet regulatory and security standards, reducing the risk of penalties and legal complications.
- Better Visibility: It improves visibility across cloud systems and operations, giving teams a clearer picture of what is happening at all times.
- Continuous Monitoring: Threats and suspicious activities are tracked around the clock, enabling teams to respond quickly when anomalies arise.
- Reduced Security Risks: A well-structured cloud security setup significantly lowers the overall risk exposure across cloud environments.
- Business Continuity: It ensures stable, uninterrupted operations, ensuring business processes continue to run even during security incidents.
- Advanced Technology Protection: Modern cloud security technologies add an extra layer of defence, keeping organizations protected against evolving and sophisticated threats.
Read More: Role of Cybersecurity in the Metaverse & Web 3.0
How Does Cloud Security Work?
Cloud security works by layering multiple protections across data, applications, and infrastructure simultaneously. Security policies define the rules. Monitoring systems watch for anything unusual. Encryption technologies make sure that even if data is intercepted, it cannot be read. Modern cloud security systems are built to respond in real time. They detect suspicious activity, identify weaknesses, and trigger responses before damage can spread. Identity and network security systems provide additional reinforcement, making the overall environment significantly harder to compromise.
Types Of Cloud Service Models
Cloud services come in different models, and each one handles security responsibilities differently. Understanding these models helps organizations know exactly what they are responsible for and what their provider covers.
| Feature | IaaS (Infrastructure as a Service) | PaaS (Platform as a Service) | SaaS (Software as a Service) |
| What It Is | Provides virtualized computing resources like servers, storage, and networking through cloud infrastructure. | Offers a platform for developers to build, test, and deploy applications without managing infrastructure. | Delivers ready-to-use software applications through the internet without installation or infrastructure management. |
| You Manage | Users manage operating systems, applications, data, and security configurations while the provider manages hardware infrastructure. | Users manage applications and data while the provider manages infrastructure, operating systems, and development tools. | The cloud provider manages infrastructure, software, security updates, and maintenance while users access the application. |
| Use Cases | Suitable for hosting websites, running applications, managing virtual machines, and scaling computing infrastructure. | Ideal for application development, testing environments, and software deployment without infrastructure complexity. | Commonly used for email services, collaboration platforms, customer relationship management, and business applications. |
| Benefits | Provides flexibility, scalability, and full control over computing resources and infrastructure management. | Accelerates development processes and reduces infrastructure management efforts for developers and organizations. | Offers easy accessibility, automatic updates, and reduced infrastructure costs for organizations. |
| Security | Security responsibilities are shared between users and providers, requiring configuration of access controls and data protection measures. | Security mainly focuses on application protection and secure coding practices within the platform environment. | The provider manages most security tasks, while users maintain strong passwords and access control policies. |
Cloud Can Face Serious Security Threats
Cloud environments face a range of security threats that can seriously disrupt business operations. Data breaches, account hijacking, insecure APIs, and poorly managed cloud resources are among the most common risks organizations deal with today. Weak identity management and inconsistent monitoring tend to exacerbate the situation. Many attacks succeed not because they are particularly sophisticated, but because basic protections were not in place. This is where cloud security solutions and technologies make a real difference, helping organizations detect threats early and respond before they escalate.
Cloud Security Solutions You Need To Know
Organizations have access to a wide range of cloud security solutions, each targeting a specific risk area.
Identity and Access Management (IAM)
I AM solutions manage who can access what across cloud systems. Through authentication, role-based access control, and identity verification, they ensure that sensitive resources are accessible only to those authorized to access them.
Data Loss Prevention (DLP)
DLP solutions monitor how data flows within cloud systems. They monitor for policy violations, flag unusual data transfers, and step in to prevent both accidental and intentional data leaks.
Security Information and Event Management (SIEM)
SIEM solutions pull security data from multiple sources across cloud environments and analyze it in one place. When something looks off, they generate alerts and help security teams respond quickly before a small issue turns into a serious incident.
Cloud Workload Protection Platforms (CWPP)
Virtual machines, containers, and other cloud workloads need their own layer of protection. CWPP solutions monitor these workloads in real time, identify vulnerabilities, and defend against attacks targeting active cloud operations.
Cloud Security Posture Management (CSPM)
Misconfigured cloud settings are a leading cause of data breaches. CSPM solutions continuously scan cloud infrastructure for configuration errors, compliance gaps, and policy violations, keeping environments secure on an ongoing basis.
Web Application Firewall (WAF)
A WAF sits in front of cloud-hosted applications and filters out harmful web traffic before it can cause damage. It blocks threats like SQL injection, cross-site scripting, and other common web-based attacks.
Cloud Security Tools
Beyond broad solutions, organizations also rely on specialized cloud security tools to handle specific monitoring, detection, and protection tasks.
Cloud Workload Protection Platforms (CWPPs)
CWPP tools cover the full range of cloud workloads, from virtual machines and containers to serverless functions. They monitor runtime activity, surface vulnerabilities, and block malicious attacks targeting active workloads.
Cloud Access Security Brokers (CASBs)
CASBs act as a checkpoint between users and cloud services. They enforce security policies, track user activity, and provide security teams with clear visibility into how cloud applications are used across the organization.
Cloud Security Posture Management (CSPM)
CSPM tools run regular scans across cloud infrastructure to catch configuration risks and compliance issues. They give organizations a clearer picture of where their security posture stands and where it needs improvement.
Secure Access Service Edge (SASE)
SASE integrates network security and access control into a single, cloud-based framework. It provides secure connectivity, data protection, and threat monitoring across distributed cloud environments, making it especially useful for organizations with remote teams or multiple locations.
Also Read: AI-Powered Cybersecurity Breakthrough: Real-Time Detection and Prevention of Cyber Attacks
How to Secure the Cloud?
Securing a cloud environment requires a combination of strong policies and the right technologies. Encryption, multi-factor authentication, regular monitoring, and vulnerability assessments all play an important role in keeping cloud infrastructure safe.
Relying on robust cloud security technologies and implementing structured cloud security solutions makes it significantly easier to maintain a secure environment and stay ahead of potential attacks.
Career Scope in Cloud Security
As cloud adoption continues to climb across industries, demand for professionals with cloud security expertise is growing just as fast. Organizations are actively seeking people who can design, manage, and improve their cloud security configurations.
Cloud Security Engineer
Cloud security engineers are responsible for building and maintaining the security controls that protect cloud environments. Their work includes configuring cloud security tools, monitoring for threats, and ensuring cloud infrastructure remains protected against known vulnerabilities.
Cloud Security Architect
Cloud security architects take a bigger picture view. They design the overall security framework for cloud environments, ensuring that every layer of protection integrates and that cloud technologies are integrated securely from the ground up.
Cloud Security Analyst
Cloud security analysts spend most of their time monitoring cloud environments and investigating anything that looks suspicious. They review security logs, identify potential threats, and work to improve how quickly and effectively their teams respond to incidents.
DevSecOps Engineer
DevSecOps engineers bring security into the development process itself rather than treating it as an afterthought. Secure coding practices, automated testing, and continuous monitoring help ensure applications are built with security baked in from the start.
Cloud Security Consultant
Cloud security consultants work with organizations to help them figure out where their cloud security gaps are and how to close them. They assess risks, recommend the right cloud security solutions, and help build protection frameworks that hold up over time.
Summing Up
Cloud computing is not slowing down, and neither are the threats that come with it. IDC projects global security spending to hit $308 billion in 2026 and cross $430 billion by 2029, which says a lot about where business priorities are heading. Over 83% of companies already consider cloud security a top concern, and that number is only going to grow as cyber threats get more sophisticated.
Whether you run a large enterprise or a small business, cloud security is something that genuinely cannot wait. Getting the right technologies, policies, and strategies in place now is far less stressful than dealing with a costly breach or major disruption down the line.
Related Links:
FAQs About Cloud Security? Definition, Types, Benefits, and Career Scope
What other practices are important for cloud security?
Regular security audits, multi-factor authentication, and data encryption are some of the most important practices for cloud security. Continuous monitoring, security awareness training, and solid backup strategies also play a big role in keeping cloud environments safe and operations running without disruption.
What are the key technologies for cloud security?
Cloud security technologies include encryption, identity and access management, security monitoring platforms, and firewalls. Cloud security posture management tools and workload protection platforms also play a key role. Together, these technologies build a strong layered defence that keeps cloud infrastructure and sensitive data protected at all times.
What are the main security risks associated with the cloud?
Data breaches, account hijacking, insecure APIs, and misconfigured storage systems are among the most common cloud security risks. Insider threats and weak monitoring practices also leave organizations vulnerable. Putting the right cloud security solutions and monitoring tools in place helps organizations detect and manage these risks effectively.
Is the cloud less secure than on-premises computing?
Not necessarily. Cloud security depends largely on how well systems are configured and managed. Many cloud providers invest heavily in advanced security controls and monitoring. When organizations follow proper practices and use reliable cloud security tools, cloud environments can be just as secure as on-premises infrastructure.
Is cloud security the same as cyber security?
They are related but not the same. Cyber security covers the protection of all digital systems and networks broadly. Cloud security is a focused part of cyber security that specifically deals with protecting cloud data, applications, and infrastructure using tools like encryption, identity management, and access control.