Applications are under attack more than ever, and the damage being done is harder to ignore. In 2024, the global average cost of a data breach reached $4.88 million, a 10% increase from the previous year and the largest year-over-year increase since the pandemic. On top of that, 98% of web applications are vulnerable to attacks that can result in malware, redirection to malicious websites, and more. The scale of the problem is only growing.
So what is application security? Simply put, it is the practice of identifying, fixing, and preventing vulnerabilities in software applications to protect them from threats and unauthorised access throughout their entire lifecycle.
In this guide, we cover everything from types of application security and common threats to the best tools, career paths, and what the future of this field looks like.
What Is Application Security?
Application security refers to the processes, tools, and practices organizations use to identify and remediate vulnerabilities in software before attackers can exploit them. It covers the full application lifecycle, from design and coding through deployment and maintenance. It is a continuous discipline that involves identifying application security vulnerabilities, addressing application security threats, and building protection into every layer of the software development lifecycle (SDLC).
Why Application Security Is Important?
The consequences of poor application security are concrete and costly. A single exploited vulnerability can expose millions of user records, trigger regulatory penalties, and cause lasting damage to an organisation’s reputation. Beyond the financial impact, application security threats are becoming more sophisticated each year, with attackers actively scanning for vulnerabilities across enterprise software and mobile apps.
Organizations that take application security seriously are better positioned to meet compliance requirements, maintain customer trust, and recover quickly when incidents occur; those that do not tend to learn the hard way how costly that decision was.
Types of Application Security
There are several distinct types of application security, each focused on protecting a different kind of software environment.
Web Application Security
Web application security focuses on protecting browser-based applications from common threats such as SQL injection, cross-site scripting, and broken authentication. Given that web applications are among the most publicly accessible systems any organisation operates, they are among the highest-risk areas for application security vulnerabilities.
Cloud Application Security
As more applications move to cloud environments, securing them requires a different approach. Cloud application security covers identity management, data protection, access controls, and configuration management across cloud-hosted systems. Misconfigurations are a leading source of application security vulnerabilities in cloud environments, making this area particularly important to get right.
Mobile Application Security
Mobile applications face their own unique set of application security threats, from insecure data storage on devices to weak communication protocols. Mobile application security focuses on protecting apps running on iOS and Android, ensuring sensitive data is handled securely, and the app behaves appropriately even on compromised devices.
API Security
APIs connect applications to external services and have become a primary target for attackers. API security is a critical component of overall application security because a poorly secured API can expose backend systems, leak sensitive data, and bypass other security controls. Proper authentication, input validation, and rate limiting are all essential components.
Container and Microservices Security
Containers and microservices have changed how most modern applications are built, bringing a new set of application security challenges. Each component must be secured individually, communication between services must be properly managed, and the architecture must be designed to prevent a compromise in one area from quietly spreading through the rest of the system.
Common Application Security Threats and Vulnerabilities
Understanding application security threats and vulnerabilities is the foundation of building effective defences.
Injection Attacks
Injection attacks happen when untrusted data is sent to an interpreter as part of a command or query. SQL injection is the best-known example, but injection vulnerabilities exist across many technologies. They remain among the most dangerous and commonly exploited application security vulnerabilities.
Broken Authentication and Session Management
When authentication mechanisms are poorly implemented, attackers can compromise passwords, session tokens, or other credentials, enabling them to take over user accounts. Broken authentication is consistently listed among the top application security threats because it can grant attackers direct access to sensitive systems and data with relatively little effort.
Cross-Site Request Forgery (CSRF)
CSRF attacks trick authenticated users into submitting requests they did not intend to make. Because the request comes from a legitimate user session, it can bypass many standard security controls. It is a subtle application security vulnerability, but it can have serious consequences when exploited.
Security Misconfiguration
Security misconfiguration is one of the most widespread application security threats, largely because it can happen at any layer of the stack. Default credentials left unchanged, unnecessary features enabled, overly permissive access settings, and missing security headers all fall into this category. Regular audits and automated scanning help catch these issues before attackers do.
Sensitive Data Exposure
Applications that handle personal information, financial data, or credentials without proper encryption and access controls put that data at serious risk. Sensitive data exposure is a category of application security vulnerabilities that includes everything from unencrypted databases to improperly cached information in browsers.
Missing Function Level Access Control
When applications do not properly enforce what different users are allowed to do, attackers can access functionality they should never be able to reach. Missing function-level access control is a common application security vulnerability in complex applications where access rules are inconsistently applied across different parts of the system.
Insufficient Logging and Monitoring
Without proper logging and monitoring, application security threats can go undetected for weeks or even months. Insufficient logging means that when something does go wrong, teams have little visibility into what happened, how far it spread, or how to prevent it from happening again.
How Application Security Works?
Application security works by layering multiple controls across different aspects of how an application operates.
Authorization
Authorization controls define what authenticated users are permitted to perform within the application. Properly implemented authorization controls guarantee that users can access data and perform operations for which they are authorized, thereby limiting the risk of privilege escalation and unauthorized access to sensitive resources.
Authentication
Authentication verifies users’ identities before granting them access to an application. Strong authentication is a foundational element of application security and typically includes multi-factor authentication, secure password policies, and session management controls that prevent unauthorized credential reuse.
Encryption
Encryption protects data both in transit and at rest, making it unreadable to anyone who intercepts it without the proper keys. It is one of the most fundamental mechanisms in application security, applied to everything from database storage to API communications and user credentials.
Logging and Monitoring
Logging records what happens within an application, and monitoring analyzes those logs in real time to detect suspicious activity. Together, they give security teams the visibility needed to identify application security threats quickly and respond before damage spreads.
Security Testing
Application security testing is the process of actively searching for vulnerabilities in an application before attackers find them. It covers a range of techniques and tools, from automated scanning to manual penetration testing, and is one of the most important ongoing activities in any application security programme.
Application Security Tools and Solutions
A wide range of application security tools and solutions is available to help organizations identify and remediate vulnerabilities across their software environments.
Static Application Security Testing (SAST)
SAST is a form of application security testing that analyzes source code for vulnerabilities without running the application. It integrates naturally into early development stages and helps identify issues such as insecure coding patterns, hardcoded credentials, and logic errors before they reach a live environment.
Dynamic Application Security Testing (DAST)
DAST is application security testing performed against a running application. It simulates real-world external attacks and surfaces vulnerabilities that only appear at runtime, making it a valuable complement to SAST in any comprehensive application security testing programme.
Interactive Application Security Testing (IAST)
IAST combines elements of both SAST and DAST by monitoring application behaviour internally during testing. It provides real-time feedback on vulnerabilities as they are triggered, delivering highly accurate, actionable findings with fewer false positives than many other application security tools.
Runtime Application Security Protection (RASP)
RASP is built directly into the application and monitors its behaviour in real time during execution. Unlike traditional application security tools that operate before or after deployment, RASP detects and blocks application security threats in real time, adapting to runtime conditions.
Mobile Application Security Testing (MAST)
MAST is a specialized application security testing method focused on identifying vulnerabilities in mobile applications. It covers areas specific to mobile environments, including insecure data storage, weak cryptography, improper session handling, and vulnerabilities in the communication between the app and backend services.
Web Application Firewall (WAF)
A WAF is one of the most widely deployed application security solutions for web-facing applications. It sits between incoming traffic and the application, filtering out malicious requests targeting known application security vulnerabilities, such as SQL injection and cross-site scripting, before they reach the application.
Cloud-Native Application Protection Platform (CNAPP)
CNAPP is a category of application security solutions designed specifically for cloud environments. It brings together cloud security posture management, workload protection, and application security testing into a unified platform, giving security teams broader visibility across cloud-native applications and infrastructure.
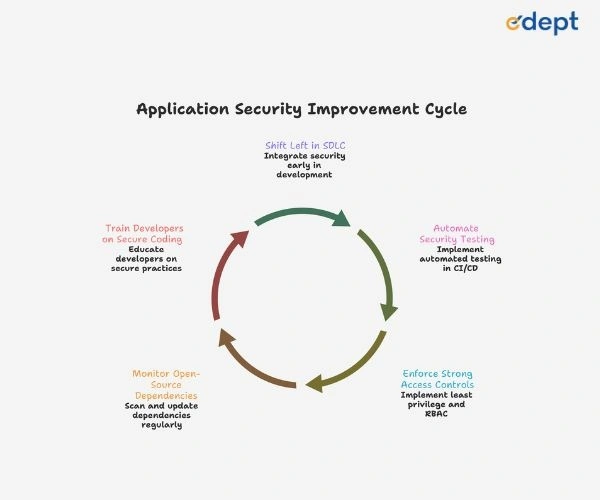
Application Security in DevOps and DevSecOps
Traditional workflows treated application security as a final step, resulting in vulnerabilities being detected late and fixed at high cost. DevSecOps changes this by integrating application security tools, testing, and security policies directly into the development pipeline. Security feedback reaches developers in real time, application security threats are addressed continuously, and fewer critical application security vulnerabilities make it into production environments.
Career Opportunities in Application Security
Demand for application security professionals is growing rapidly as organizations invest more heavily in protecting their software environments.
Application Security Engineer
Application security engineers design and implement the controls, processes, and application security tools that protect software systems. They work closely with development teams to identify application security vulnerabilities, review code for security issues, and build security into the software development lifecycle from the ground up.
Security Analyst
Security analysts monitor applications and infrastructure for signs of application security threats, investigate incidents, and improve detection and response capabilities. They spend significant time working with logs, alerts, and application security solutions to understand what is happening across the organization’s software environment.
DevSecOps Engineer
DevSecOps engineers bridge the gap between development, security, and operations. They build and maintain automated application security testing pipelines, enforce security policies across CI/CD workflows, and ensure application security solutions are integrated into how software is built and deployed every day.
Penetration Tester
Penetration testers take an attacker’s perspective, actively probing applications for security vulnerabilities before real attackers do. They use a combination of manual techniques and specialized application security tools to simulate real-world attacks and provide organizations with detailed findings they can act on.
The Future of Application Security
Application security is evolving fast. AI-powered application security tools are improving at detecting vulnerabilities and predicting emerging threats. Cloud-native architectures, microservices, and API-driven development are expanding the attack surface that application security solutions need to cover. Regulatory pressure is growing, too. The future belongs to teams that treat application security as a continuous, automated, and deeply integrated part of their software development process.
Final Thoughts: Why Application Security Can No Longer Be an Afterthought
The real cost of ignoring application security only becomes obvious after something has already gone wrong. Forrester Research found that fixing application security vulnerabilities early in development costs up to 30 times less than addressing them in production. That is a number worth paying attention to.
The case for application security goes beyond technology. It is about protecting your business, meeting regulatory requirements, and maintaining user trust. Knowing the application security controls relevant to your environment, staying ahead of emerging threats, and using the right tools help you build software people can trust.
FAQs on Application Security: Complete Guide to Tools, Benefits, and Career Scope
What is application security testing?
Application security testing is the process of identifying vulnerabilities in software applications before attackers can exploit them. It includes techniques like static analysis, dynamic testing, and interactive testing, each examining the application from a different angle. Regular application security testing is one of the most effective ways to detect and fix weaknesses before they cause real damage.
What are the most common application security risks?
The most common application security risks include injection attacks, broken authentication, security misconfiguration, sensitive data exposure, and insecure APIs. These application security vulnerabilities appear consistently across web, mobile, and cloud environments. The OWASP Top 10 is a widely referenced resource that helps teams understand and prioritize the application security threats most likely to affect their software.
How does application security protect sensitive data?
Sensitive data does not protect itself, and that is exactly what application security is designed to address. Encryption ensures that even intercepted data is unreadable to anyone who intercepted it. Access controls prevent unauthorized users from accessing it. Application security testing finds the vulnerabilities that could expose it before attackers do. Together, these application security solutions provide layers of protection for the data applications used every day.
How does DevSecOps improve application security?
DevSecOps improves application security by integrating application security testing and security controls directly into the development and deployment pipeline. Rather than treating security as a final checkpoint, DevSecOps makes it a continuous part of the software development lifecycle. This approach detects application security vulnerabilities earlier, accelerates remediation, and reduces the number of issues that reach production environments.
What are the benefits of implementing application security solutions?
Implementing application security solutions reduces the risk of data breaches, lowers remediation costs by catching application security vulnerabilities early, supports regulatory compliance, and builds user trust. Organizations with strong application security programmes are better prepared to respond quickly and effectively to application security threats, limiting damage when incidents occur and maintaining operational stability over the long term.