Malware analysis is the process of examining malicious software to determine its origin, functionality, and potential impact, enabling security teams to detect, mitigate, and prevent cyber threats.
Cybersecurity is an integral part of the technical domain in today’s world. With millions of data points being processed every day online, cybersecurity acts as a safety barrier to safeguard the data. Still, attackers are getting modernized too as time passes, using modern attacks. Attacks like phishing, malware attacks, and identity theft are among the most famous cybercrimes. Cybersecurity professionals follow certain steps to prevent these attacks from infecting the systems. Malware analysis is one of the methods that prevents systems from getting infected by malware software or files.
What is Malware?
Malware is a form of malicious software, referring to any program specifically designed to harm and exploit networks and data. It includes viruses, ransomware, spyware, and other harmful programs that operate without user consent.
Cyber attackers use malware as it is the easiest and fastest way to breach a system. According to the Annual Cyber Threat Report 2024-25 published by the Australian Government, nearly 46% of cyber incidents involve malware and ransomware, which shows how rapidly the threats are evolving.
Having good knowledge about what malware actually is before starting on the journey of learning about malware analysis in cybersecurity. Without good knowledge of what you have to analyze, you will eventually fail.
The different types of malware
There are a variety of malware, each specifically designed with a specific goal of its own. Knowing these types of malware attacks will help you understand how they actually work, their attack patterns, so you can learn steps to neutralize them.
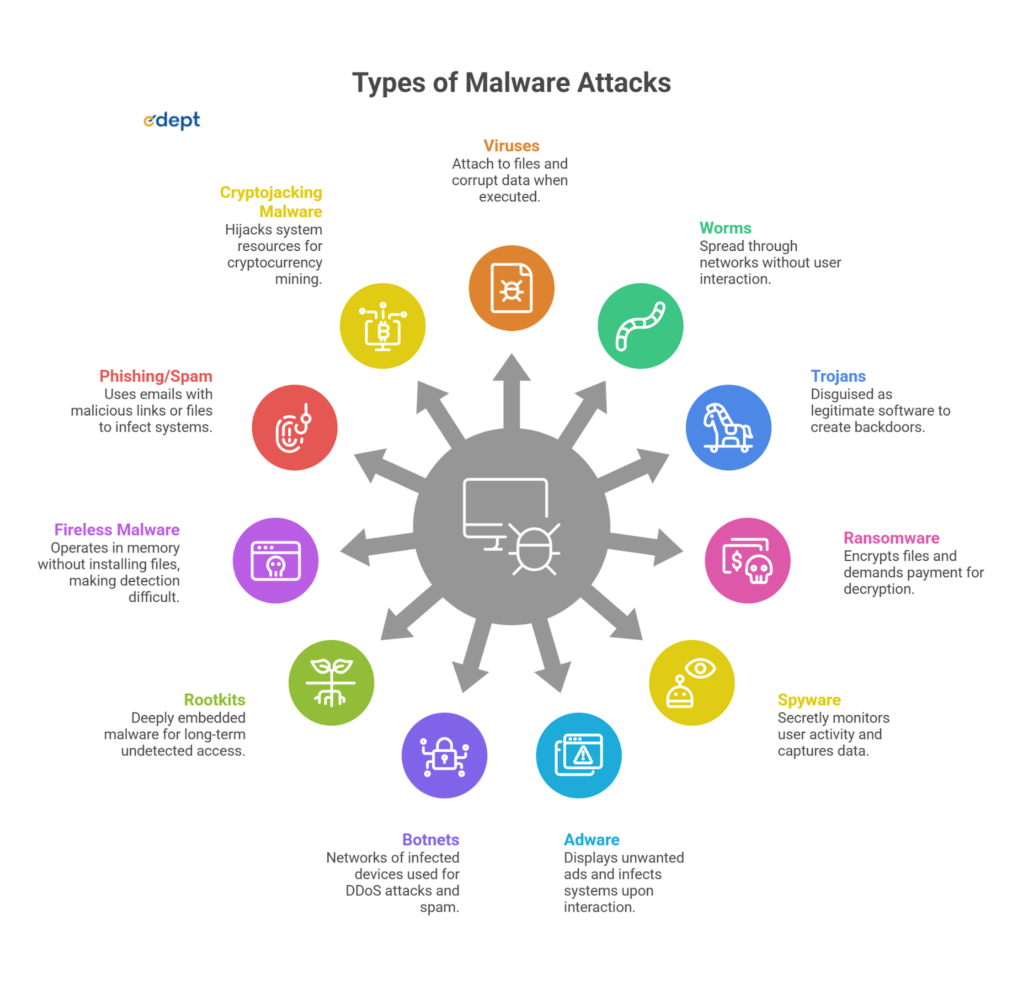
Viruses
Viruses are like leeches that attach themselves to files and spread when those files are executed. Their main task is to corrupt data and delete it with user action.
Worms
Unlike viruses, worms spread through the networks without user interaction. They exploit vulnerabilities and infect the systems.
Trojans
These are basically malware disguised as legitimate software. They secretly create backdoors for attackers and don’t self-replicate like viruses.
Ransomware
This is the most dangerous type of malware attack. Ransomware attacks files, encrypts them, and in return demands payment as ransom. Globally, ransomware is known to be the main reason behind the highest financial losses for organizations and businesses.
Spyware
Spyware secretly monitors user activity, capturing keystrokes, passwords, and other personal data.
Adware
As the name suggests, adware displays unwanted ads to attract users, and when interacted with, it will infect your system. Though this is less harmful, it can seriously affect performance and privacy.
Botnets
A botnet is a set of networks of infected devices interconnected and controlled remotely. Attackers use these devices for DDoS attacks and spam campaigns.
Rootkits
Rootkits are hard to track as they lie deep inside the systems, allowing attackers to maintain long-term access without detection.
Fireless Malware
Another malware, like rootkits, fireless malware operates in memory without installing files, making it harder to detect with traditional tools.
Phishing/Spam
These are one of the most famous types of malware attacks. Phishing, though, is not always software-based. It uses emails to send malware through clickable links or files, and infect the systems when clicked on.
Cryptojacking Malware
This malware hijacks system resources to mine cryptocurrency without the user even knowing about it.
What is Malware Analysis?
We saw what malware is, what the different types of malware are, and how they affect systems and steal data. Now, let’s talk about malware analysis. It is a process of studying malware to understand how it works, the damage it can incur on the systems, and how to neutralize it. This whole process is the core part of malware analysis in cybersecurity, letting professionals respond to threats effectively.
Instead of just removing malware from the systems, analysis investigates:
- How the malware actually entered the system
- What actions does it perform when inside the system
- How malware communicates with attackers, sending them the stolen data
This helps build defenses and prevent future attacks.
Also read: Is Cybersecurity a Good Career?
Types of Malware Analysis
Now that malware has variations, malware analysis has different approaches depending on the situation. Let’s look at some of these types of malware analysis.
Static Analysis
In static malware analysis, the malware is examined without being executed first. Analysts study the malware’s code and structure to check its safety.
Dynamic Analysis
Analysts run malware in controlled environments, also known as sandboxes, and observe its behavior in real time and the patterns it reflects.
Memory Analysis
Its sole focus is on analyzing system memory to detect any hidden abnormal files or fileless malware.
Reverse Engineering
In this process, engineers crack down the malware code to the core to understand its logic and functionality.
Malware Unpacking
Many malware have hidden files inside, which are packed or obfuscated. Unpacking them reveals what their source codes are for actual analysis.
Benefits of Malware Analysis
Malware analysis plays a crucial role in safeguarding organizations’ data against these attacks. It helps businesses in:
- Detecting potential threats early
- Understand the exact attacker behavior
- Improving the security systems using feedbacks
- Prevent future breaches
According to IBM, the average cost of a data breach is $4.45 million, making active malware analysis crucial. It also supports threat intelligence and helps teams stay ahead of modern cyber threats.
Start your Cybersecurity Career with Edept and secure your Digital Future
The use cases for malware analysis in Cybersecurity
There is a big list of malware use cases across multiple areas. Let’s look at and understand some of them.
Incident response
Quick response against attacks to investigate breaches and neutralize them.
Malware research and detection
Continuous research on modern malware attacks and new threats is essential to improve antivirus and security tools over time.
Indicator of Compromise (IOC) extraction
Extracts data like IPs, domains, and file hashes to understand attack patterns, which is beneficial to detect similar attacks in the future.
Threat hunting
Enables a constant search procedure for any hidden threats inside systems.
Malware Analysis in Cybersecurity Careers
Malware analysis in cybersecurity is a high-value skill creating opportunities for aspirants across multiple roles globally. With cybercrime projected to cost $10.5 trillion annually, organizations need professionals who can understand and respond to these attacks efficiently. Let’s look at some career choices people make when entering this domain in the context of malware analysis.
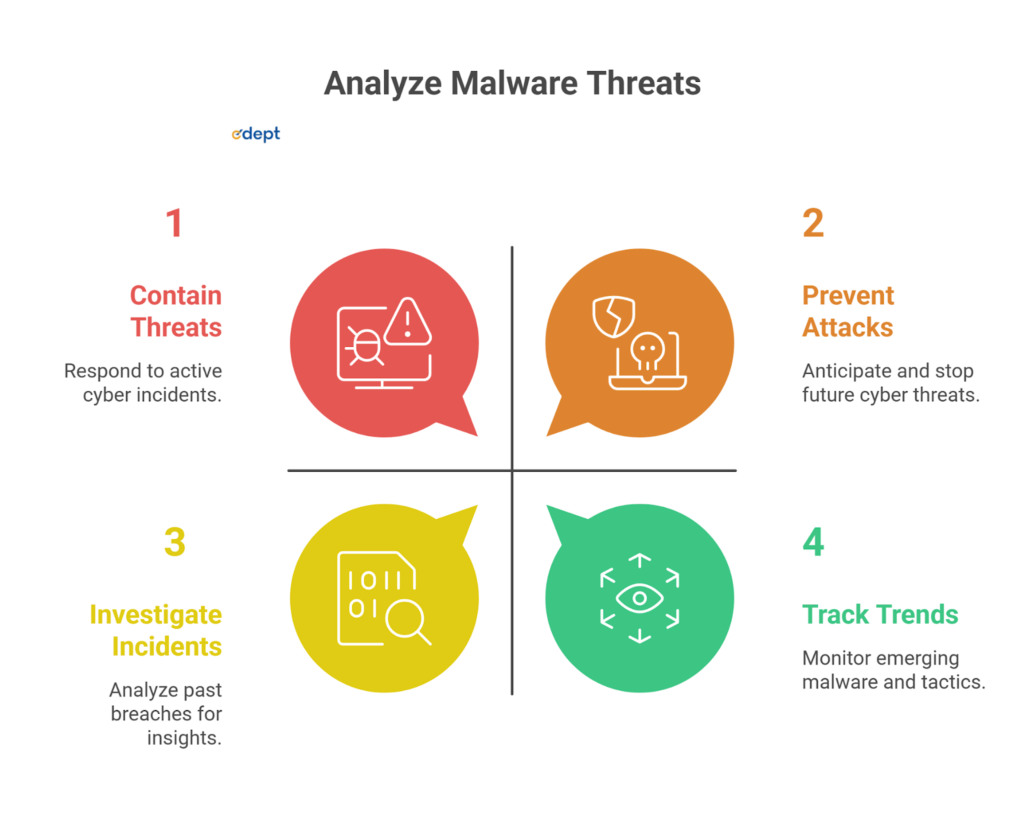
Security Operations Center (SOC) Analysts
SOC analysts monitor alerts and investigate any suspicious activities in the server. If anything serious is noted, they use malware analysis to contain threats in real time.
Digital Forensics & Incident Response (DFIR)
DFIR professionals are known to analyze malware after an attack, to trace where it originated from, and help the organizations recover from these breaches.
Penetration Tester (RED Team)
Ethical hackers study malware behavior in order to simulate real-world attacks to understand the system vulnerabilities and cure them before attackers do.
Threat Intelligence Analysts
Their main task is to track any emerging malware trends and analyze their new working tactics to be ready with their modernized defenses.
Challenges in Malware Analysis
With attackers using modern malware variants and strategies, traditional malware analysis is becoming increasingly complex. Modern malware often employs threats through operations like encryption, obfuscation, and polymorphism. These make it very difficult for analysts to track the attacks and stop them from spreading. Fireless malware is another layer of difficulty for professionals as it operates entirely in the memory with no traces left.
Additionally, attackers design malware to detect sandbox environments to prevent dynamic malware analysis from having any effect. Analysts also require specialized tools and isolated environments, which are dependent on resources. With constantly evolving malware dynamics, it’s really tough for organizations to catch up with them and safeguard their data.
Future of Malware Analysis (AI & Automation)
Automated malware analysis has recently experienced a surge in growth due to the advancement in AI technology and the machine learning sector. The ability for researchers to use both manual and analytical methods to analyze threats is becoming obsolete, given the increasing number of new malware samples every day. Machine learning techniques are able to quickly detect trends or anomalies in large volumes of information and categorize threats in real-time.
Automated sandboxing and behavioral analysis tools are also becoming standard in modern security systems, which, in time, improves response speed. Though even with advancements in AI technology, human expertise still remains at the top to stop advanced and targeted attacks. This makes AI a powerful assistant of a professional, not their replacement in cybersecurity.
Related Links:
| Real-Life Cyberattack Case Studies | Key Cybersecurity Interview Questions |
| Role of AI in Cybersecurity | Ethical Hacking Tools Guide |
FAQS
Why is malware analysis important?
Malware analysis is important to identify malware attacks in real-time and stop them from spreading and infecting the whole system.
What is the goal of malware analysis?
The main goal of malware analysis is to determine how malware works, how it spreads throughout the server, and how to neutralize it in real-time.
Can malware analysis be automated?
Yes, with current advancements in AI and automation tools, malware analysis can be automated, but human expertise is required to assist.
What are the challenges of malware analysis?
Some major challenges faced by malware analysis professionals are encryption, obfuscation, and constantly evolving malware techniques, making it difficult to analyze malware.
Who performs malware analysis?
Cybersecurity professionals such as SOC analysts, DFIR experts, and threat intelligence analysts handle malware analysis.
What skills are required for malware analysis?
Good knowledge of programming, networking, and cybersecurity fundamentals, along with an operating system, is key to malware analysis.
What is the difference between malware and a virus?
A virus is a type of malware that attacks files and software, while malware is a broader term that includes many other threats, including viruses like ransomware and spyware.