Prepare for your first cybersecurity interview with confidence. This beginner-friendly guide covers essential questions, core concepts, tools, and practical tips. Learn what recruiters expect, improve your fundamentals, and build the skills needed to succeed in entry-level cybersecurity roles.
Breaking into the cybersecurity space can feel overwhelming, especially when you are preparing for your first interview. Entry-level cybersecurity interviews mainly focus on testing your fundamentals, logical thinking, and practical awareness rather than having in-depth expertise. Recruiters check if you really have practical knowledge of cybersecurity concepts, good communication skills, and a genuine interest in the field. In this guide, we will cover the most common cybersecurity interview questions for beginners, along with short, structured answers to help you respond professionally and confidently in hiring trends.
What Recruiters Look for in Entry-Level Cybersecurity Candidates
Recruiters generally look for strong fundamentals in networking and security concepts. Basic tool familiarity and problem-solving ability. They hire candidates who have a good understanding of handling real-world threats, communicate clearly, and show curiosity to learn. Certifications, lab practice, and small security projects strengthen your profile. Most importantly, recruiters check whether you have an analytical or ethical mindset and are eager to grow in cybersecurity.
Read more: Cybersecurity Career Roadmap 2026
Basic Cybersecurity Fundamentals Questions
We will go through a set of questions that will test your understanding of core security principles. Keep answers simple, structured, and practical.
What is Cybersecurity?
Cybersecurity is a practice of protecting systems, data, and networks from unauthorized access and attacks causing damage. It revolves around technologies, processes, and policies designed to prevent cyber threats. The goal is to ensure the confidentiality, integrity, and availability of information.
What are the CIA Triad Principles?
The CIA triad stands for Confidentiality, Integrity, and Availability. Confidentiality ensures the safety of data by allowing only authorised users to access it. Integrity ensures data is accurate and not altered. Availability ensures systems and data remain accessible when needed.
Difference between Vulnerability, Threat, and Risk?
Vulnerability is basically a weakness in a system that attackers can use to attack. Threats are potential attacks that can exploit this weakness/vulnerability of the system. Risk is the potential damage caused if a threat successfully exploits the vulnerability.
What is Encryption? Difference Between Symmetric & Asymmetric Encryption?
Encryption converts readable data into an unreadable form to protect it from attackers. Symmetric encryption uses a single key for both encryption and decryption. Asymmetric encryption uses two keys – a public key and a private key.
Networking & Security Questions
Attackers generally target networks because most vulnerabilities are there. Thus, strong networking skills are essential in cybersecurity. Interviewers often test your understanding of protocols and network protection tools.
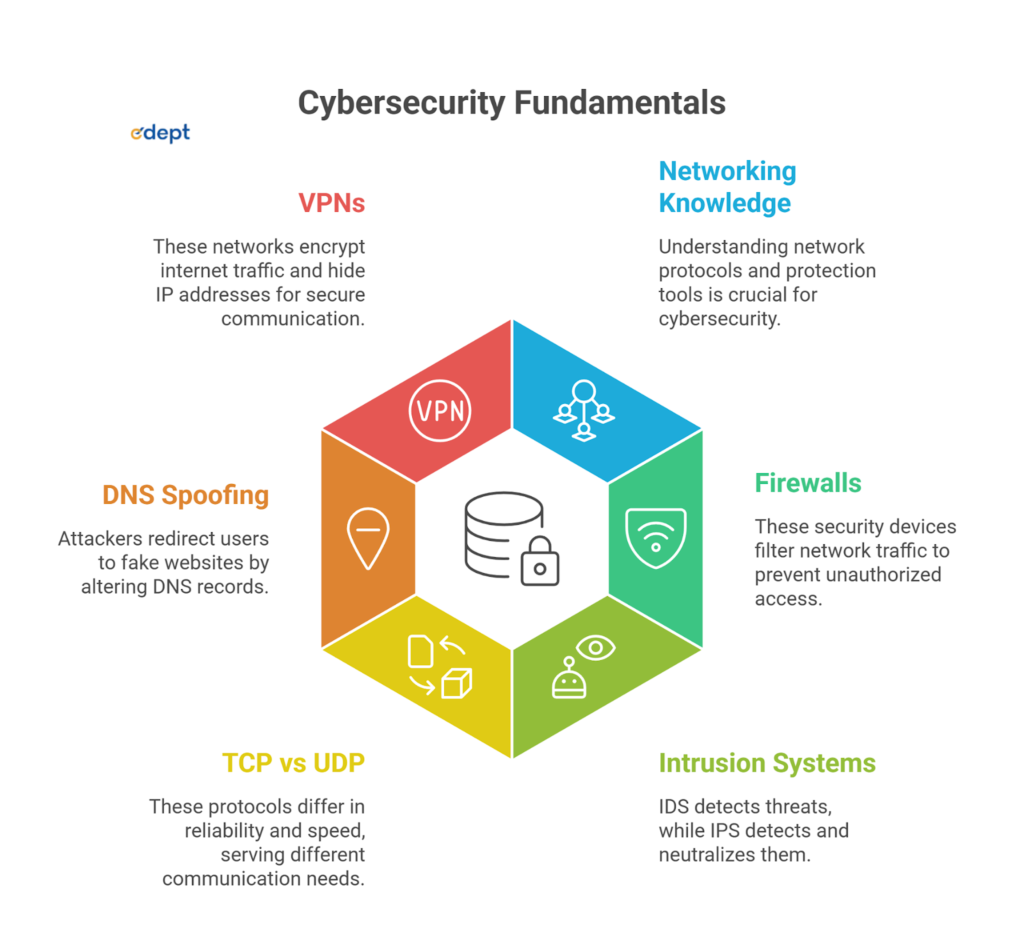
What is a Firewall?
A firewall is a security device or software that monitors and controls both incoming and outgoing network traffic, basically filtering traffic based on predefined security rules. It is the first line of defense against unauthorised access.
What Are IDS and IPS?
IDS stands for Intrusion Detection System. It monitors traffic and alerts when suspicious activity is detected. IPS stands for Intrusion Prevention System. In comparison to IDS, it not only detects threats but also neutralises them by blocking them automatically.
Explain TCP vs UDP
TCP is connection-orientated and reliable, ensuring data delivery. UDP is connectionless and faster, but does not guarantee delivery. TCP is used for secure communications, while UDP is mainly used for streaming.
What is DNS Spoofing?
DNS spoofing is a type of attack where attackers redirect users to fake websites by altering DNS records. It is used to steal credentials or distribute malware. It is also termed as DNS cache poisoning, as it poisons a DNS resolver’s cache with false IP addresses and steals sensitive information, spreads malware, and impersonates trusted sites.
What is a VPN?
VPN stands for Virtual Private Network. A VPN encrypts internet traffic and hides your IP address by creating a secure tunnel between your device and the internet.
Also read: Best Countries for Cyber Security Jobs in 2026
Ethical Hacking & Attack-Based Questions
Interviewers test your depth of knowledge in common cyber attacks and basic defence strategies. You should be able to explain the type of attack, how hackers start the attacks, and also how it impacts systems or users. When answering their question, always mention one or two prevention techniques in your answer. The response should be concise, simple, structured, and focused on practical awareness.
What is Phishing?
Phishing is a type of social engineering attack where attackers trick users into revealing sensitive information. Attackers use fake emails or websites as a medium for attacks. Prevention includes email filtering, user awareness training, and multi-factor authentication.
What is a DDoS Attack?
DDoS stands for Distributed Denial-of-Service attack, which floods a system with massive traffic. It makes services unavailable to legitimate users. Using traffic filtering and DDoS protection tools helps prevent it.
What is SQL Injection?
SQL injection occurs when attackers insert malicious SQL queries into input fields. It can give unauthorised access to databases. Prevention includes input validation and parameterised queries.
What is XSS?
Cross-site scripting allows attackers to inject malicious scripts into web pages.
It can steal session cookies or user data.
Proper input sanitisation and output encoding prevent XSS.
What is A Man-in-the-Middle Attack?
In an MITM attack, an attacker secretly intercepts communication between two parties.
It is often used to steal sensitive data. Using HTTPS and strong encryption helps prevent this attack.
Tools-Based Questions (Very Important for 2026)
Practical tool knowledge is highly valued in interviews. Recruiters expect at least basic familiarity with common security tools. Explain what the tools do and where they are used. Mention lab practice or beginner-level hands-on exposure.
Have You Used Wireshark?
Wireshark is basically a network packet analyser. It captures and inspects network traffic. It helps identify suspicious activity in a lab environment.
What is Nmap?
Nmap is a network scanning tool. It identifies open ports and running services. It is commonly used for vulnerability assessment.
What is Metasploit?
Metasploit is a penetration testing framework. It is used to test system vulnerabilities in labs. Beginners use it for ethical hacking practice.
What is Burp Suite?
Burp Suite is a comprehensive software tool developed by PortSwigger for web application security testing, penetration testing, and vulnerability assessment. It acts as an intercepting proxy between a web browser and a target web server, allowing security professionals to capture, inspect, modify, and replay HTTP/HTTPS requests and responses in real time.
Scenario-Based Cybersecurity Interview Questions
Scenario-based questions evaluate your problem-solving ability and professional thinking. Interviewers expect a calm, step-by-step response. Always mention containment, analysis, and prevention in your approach. Structured responses reflect maturity and incident-handling awareness.
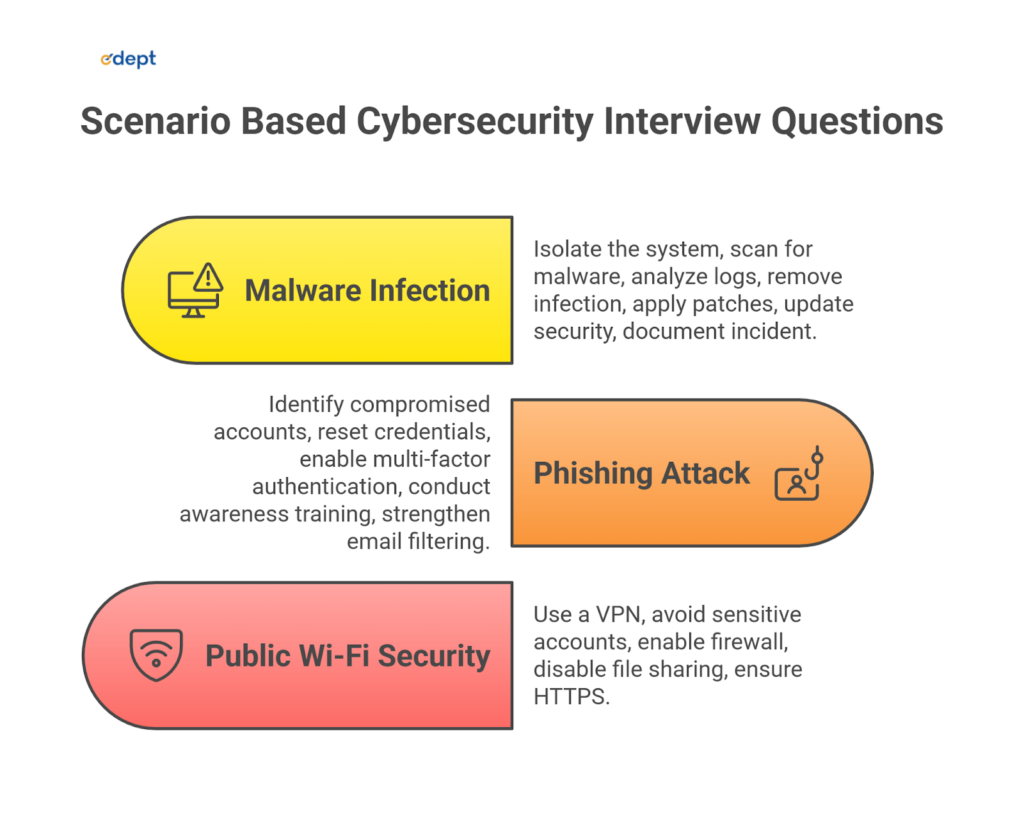
What will you do if a system is infected with malware?
First, isolate the affected system from the network to prevent further spread. Next, conduct a thorough malware scan and analyze logs to identify the infection source. After removal, apply patches, update security controls, and document the incident for reporting and future prevention
How would you respond to a phishing attack in your company?
Immediately identify compromised accounts and restrict access to prevent further damage. Reset affected credentials and enable multi-factor authentication for enhanced protection. Finally, conduct awareness training and strengthen email filtering systems to reduce future phishing risks.
Start Your Management Career with Job-Ready Skills
How do you secure a public Wi-Fi connection?
Use a reliable VPN to encrypt internet traffic and prevent interception. Avoid accessing sensitive accounts, such as banking or corporate systems, on public networks. Enable firewall protection, disable file sharing, and ensure websites use HTTPS encryption.
Secure the Digital Future: Become a Cyber Security Guardian by enrolling in the B.Voc. in Cybersecurity program by Shree LR Tiwari College of Engineering.
-> Click here!
HR + Behavioral Cybersecurity Questions
Behavioural questions assess your motivation, ethical mindset, and long-term commitment to cybersecurity. Recruiters look for passion, curiosity, and a willingness to continuously learn. Your answers should reflect confidence and professional growth. Demonstrating a proactive attitude toward skill development leaves a strong positive impression.
Why do you want to join cybersecurity?
I am passionate about protecting digital systems and solving complex security challenges. Cybersecurity offers continuous learning opportunities and real-world impact. It allows me to contribute to building safer digital environments while growing technically and professionally.
What certifications are you planning?
I plan to begin with foundational certifications like CompTIA Security+ to strengthen core concepts. After gaining experience, I aim to pursue CEH or cloud security certifications. These credentials validate structured learning and industry readiness.
How do you stay updated?
I regularly follow cybersecurity blogs, threat intelligence reports, and industry updates. I practise through labs and participate in capture-the-flag challenges. Continuous learning ensures I stay aligned with emerging cyber threats and technologies.
Describe a security project you worked on
I conducted a vulnerability assessment using tools like Nmap in a lab environment. I identified open ports, analysed potential risks, and documented findings clearly. I then recommended remediation steps to strengthen the overall security posture.
How to Prepare for Entry-Level Cybersecurity Interviews
Preparing for entry-level cybersecurity interviews requires a strong balance of fundamentals and hands-on practice. Focus on understanding core networking and security concepts before diving into advanced topics. Practice commonly used security tools in lab environments and be ready to explain how you used them. Consistent mock interview practice will help you structure answers clearly and confidently.
Networking Basics
Build a solid understanding of TCP/IP, the OSI model, ports, protocols, DNS, and basic network troubleshooting. Networking is the backbone of cybersecurity, and many interview questions are built around these core concepts.
Security Fundamentals
Revise the CIA triad, encryption types, authentication methods, common attack types, and basic risk management principles. Clear conceptual understanding helps you answer both technical and scenario-based questions effectively.
Tools Practice
Gain hands-on experience with tools like Wireshark, Nmap, Burp Suite, and basic SIEM platforms in virtual labs. Be prepared to explain what the tool does and how you applied it in practice.
Mock Interviews
Practice answering questions in a structured and professional manner. Record yourself or participate in peer mock sessions to improve clarity, confidence, and time management during real interviews.
Conclusion
Preparing for entry-level cybersecurity interviews requires more than memorising definitions. Strong fundamentals, practical exposure, and structured thinking make a real difference. Recruiters value candidates who can explain concepts clearly and apply them logically. Consistent hands-on practice with tools builds technical confidence. Stay updated, practise regularly, and approach interviews with a calm, professional mindset. With the right preparation and persistence, securing your first cybersecurity role becomes an achievable goal.
Related Links: